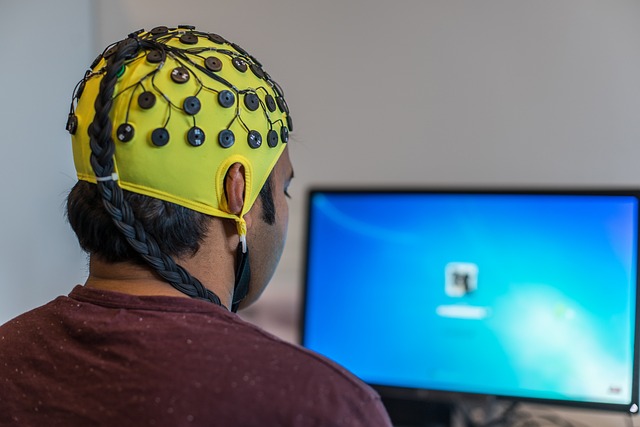
In an era where data breaches and ransomware attacks grow in sophistication, the concept of threshold sensors has emerged as a pivotal tool for defenders. These devices, often embedded in network hardware or even wearable technology, monitor activity against predefined limits and trigger alerts when patterns deviate from the norm. Their value lies not only in detecting malicious intrusion but also in reinforcing a culture of responsible digital behavior. As society becomes increasingly interconnected, the deployment of threshold sensors aligns with evolving technology etiquette and social trends that prioritize privacy, accountability, and collective safety.
Threshold Sensors: A Modern Security Layer
Threshold sensors function as sentinel thresholds across a wide spectrum of digital environments—from enterprise firewalls to consumer smart home devices. By continuously measuring parameters such as packet rates, authentication attempts, or device proximity, these sensors generate real‑time analytics. When activity crosses a set threshold—say, more than ten failed login attempts in a minute—a policy can automatically lock the account or route traffic for deeper inspection. The adaptability of threshold sensors means they can be fine‑tuned to context: a high‑volume trading platform may tolerate burst traffic differently from a medical records system that requires stricter limits. This contextual sensitivity is what makes threshold sensors indispensable in modern cyber defense architectures.
The Rise of Social Trends in Cybersecurity
Cybersecurity is no longer a purely technical discipline; it now mirrors the social fabric that shapes how we interact with technology. Current social trends emphasize transparency, shared responsibility, and the democratization of data control. People are increasingly aware that their online actions contribute to a larger digital ecosystem. Consequently, security frameworks must evolve to accommodate community‑driven norms. Threshold sensors fit neatly into this paradigm by providing a measurable, auditable layer of oversight that aligns with societal expectations for privacy and security. By setting and communicating clear thresholds, organizations demonstrate a commitment to respectful data stewardship that resonates with modern users.
Digital Footprints and Behavioral Patterns
Every click, every keystroke creates a digital footprint that, when aggregated, reveals behavioral patterns. Threshold sensors capture these micro‑behaviors, allowing security teams to differentiate between normal and anomalous activity. For example, a sudden spike in outbound data volume could indicate exfiltration, while repetitive failed authentications might signal credential stuffing. By mapping such patterns against known threat vectors, threshold sensors add a proactive dimension to threat detection. Importantly, they also provide insight into legitimate user behavior, reducing false positives and fostering trust between users and security systems.
Data Aggregation and Anomaly Detection
The power of threshold sensors is amplified when paired with data aggregation and anomaly detection algorithms. These algorithms learn baseline activity for each user or device and set dynamic thresholds that adjust over time. If a user’s device suddenly starts sending data to an unfamiliar geographic region, the sensor flags the anomaly, prompting a security review. Such capabilities are particularly relevant in remote work scenarios, where the boundary between personal and professional data blurs. By continuously learning and adapting, threshold sensors help maintain a balance between operational flexibility and risk mitigation.
Technology Etiquette in the Age of Sensors
As devices become smarter, the question of appropriate usage—technology etiquette—gains prominence. The proliferation of threshold sensors introduces a new layer of etiquette: users must understand the limits imposed by these sensors and respect them. Clear communication about what constitutes acceptable behavior, how thresholds are defined, and how breaches are handled is essential. Transparency builds confidence and encourages compliance, reducing the likelihood of accidental violations that could otherwise compromise security. In this way, technology etiquette transforms from a set of best practices into an integral part of the cybersecurity ecosystem.
Responsible Deployment of Threshold Sensors
Deploying threshold sensors responsibly involves several key steps. First, stakeholders must conduct a risk assessment to identify which assets and data flows warrant monitoring. Second, thresholds should be set in collaboration with operational teams to avoid over‑restriction that hampers productivity. Third, sensor placement should consider privacy implications—monitoring personal devices, for instance, requires explicit consent. Finally, continuous evaluation ensures that thresholds remain relevant as business processes evolve. By following these principles, organizations can harness the protective benefits of threshold sensors without creating new friction points.
User Privacy and Consent
Privacy concerns are central to the adoption of any monitoring technology. Threshold sensors collect granular data, which can be perceived as intrusive if not handled correctly. Best practice dictates that users are informed about the scope of monitoring, the data collected, and the purposes served. Consent mechanisms—such as opt‑in agreements for personal devices—are essential to comply with regulations like GDPR or CCPA. Moreover, data anonymization techniques can be employed to ensure that only aggregated insights are used for security decision‑making, thereby protecting individual identities while still benefiting from threshold-based anomaly detection.
Integrating Threshold Sensors with Existing Protocols
Effective cybersecurity requires seamless integration across multiple layers of defense. Threshold sensors complement established protocols such as SIEM (Security Information and Event Management), IDS/IPS (Intrusion Detection/Prevention Systems), and zero‑trust architectures. By feeding real‑time alerts into SIEM dashboards, security teams can correlate sensor events with broader threat intelligence. Similarly, threshold sensors can serve as the first line of defense, automatically triggering IP block lists or quarantine actions before they reach downstream systems. This tight integration enhances situational awareness and enables faster, more accurate response times.
Case Study: Smart Office Environments
In a typical smart office, threshold sensors are embedded in access control systems, network switches, and even individual workstations. For instance, a sensor may detect an unusual pattern of badge swipes at night, triggering an immediate lockdown. When integrated with the company’s SIEM, such an alert can be cross‑checked against known security incidents, allowing analysts to distinguish between a legitimate after‑hours maintenance task and a potential breach. The real‑time nature of threshold sensors ensures that even brief windows of vulnerability are identified and closed before exploitation can occur.
Future Outlook and Emerging Standards
The next decade promises to expand the capabilities of threshold sensors through AI‑driven predictive analytics and edge computing. As standards bodies like NIST and ISO develop guidelines for sensor deployment, organizations can adopt best practices that guarantee interoperability and compliance. Emerging trends also include the use of blockchain for immutable audit trails, ensuring that threshold sensor logs cannot be tampered with. Such advancements will not only bolster technical defenses but also reinforce public trust in the responsible use of monitoring technologies.
Conclusion: A Harmonious Blend of Security and Social Responsibility
Threshold sensors represent more than a technological upgrade; they embody a shift toward a security culture that respects individual rights while protecting collective assets. By aligning sensor thresholds with social trends—such as transparency and shared responsibility—and embedding them within a framework of technology etiquette, organizations can create resilient defenses that adapt to evolving threats. The future of cybersecurity hinges on this harmonious blend of technical rigor and social consciousness, ensuring that every data point, no matter how small, contributes to a safer digital ecosystem.